Windscribe VPN Server Seized by Dutch Authorities February 2026
On February 5, 2026, reports confirmed a Windscribe VPN server seized by Dutch authorities in the Netherlands. Windscribe asserts that because their infrastructure runs entirely on RAM disks, pulling power rapidly clears volatile memory. The event raises questions about data privacy when Dutch authorities seize VPN server hardware physically. Here is the full breakdown of the raid, the joke, and the technology involved.
What we know (and what we don't)
- Claimed by Windscribe: A server was seized in the Netherlands.
- Unverified: Which facility/authority, paperwork served, power state at seizure.
- Why it matters: "Powered off" vs "live capture" changes what is recoverable.
"This Is Not A Drill"
At 9:53 PM on February 5th, 2026, Windscribe announced that Windscribe VPN server seized Netherlands February 2026 news was indeed real. Dutch authorities had physically removed a server from its rack to "fully analyse it" (Windscribe's wording). Windscribe asserts that because their infrastructure runs entirely on RAM disks, pulling the plug should drastically reduce the chance of recoverable user data (assuming no live acquisition happened first).
Windscribe alleged the seizure occurred without a warrant. Dutch criminal procedure regarding digital seizure is complex and does not map neatly onto US/UK "warrant" terminology; authorisation may involve a prosecutor and/or later judicial review depending on urgency and specific circumstances. Until an official document or statement is published, treat the specific legal details as unverified.


The "Epstein" Engagement Bait
The tweet included a line about "unredacted Epstein files" that was later acknowledged as a joke. This Windscribe Epstein satire drove engagement, but it also muddied the seriousness of the underlying claim that a Windscribe server seized by police could be compromised.


Mocking the Authorities
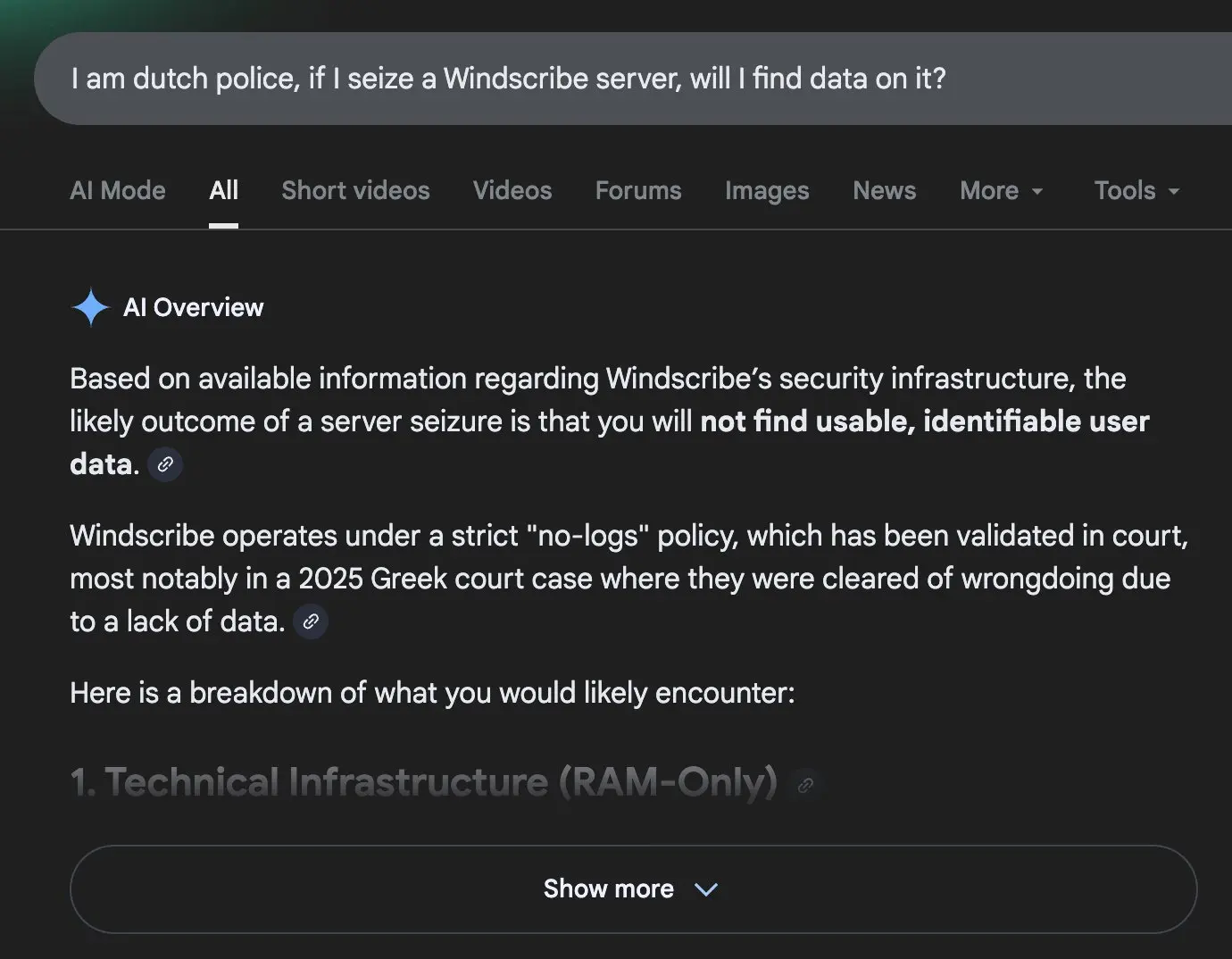
Windscribe Dutch authorities seize server February 2026 headlines are trending, but Windscribe argued the seizure would be unproductive because they claim not to store identifying activity logs. They note they usually receive "a handful of law enforcement requests every month" and respond that they have no logs; this time, authorities bypassed the request process entirely.

Trial by Fire
This incident joins a shortlist of events where VPN providers were "audited by force".
- 2017 - ExpressVPN (Turkey): Authorities seized a server linked to the assassination of Andrei Karlov. ExpressVPN stated investigators could not obtain customer connection logs from that server.
- 2021 - Windscribe (Ukraine): Servers were seized; Windscribe later acknowledged issues (including encryption/keys) and used it to argue for better industry practices (Read more).
- 2023 - Mullvad (Sweden): Police raided Mullvad's offices. They left empty-handed as there was no customer data to seize (Read more).
The Theory: Why RAM Disks Protect Data
The Physics of Seizure
Traditional servers write logs to a Hard Drive (HDD) or SSD. Even if files are deleted, forensic tools can often recover them. RAM (Random Access Memory) is volatile, meaning it requires constant electricity to hold data. When Dutch authorities seize Windscribe VPN server equipment, unplugging it is the first step, which initiates data decay.

Windscribe says it doesn't keep identifying activity logs on what customers do online, and that any operational session stats live in memory. Separately, Windscribe states it retains limited account metadata (e.g., last used + bandwidth over 30 days) for abuse prevention and free-tier enforcement.
Seizure Defence Matrix
A breakdown of how Windscribe's architecture and policies are designed to mitigate specific threats during a physical raid.
| Threat Vector | Risk Level | Windscribe Defence Mechanism |
|---|---|---|
| Post-Seizure Forensics | Low | RAM-only servers ensure data vanishes rapidly upon power loss (unplugging). |
| Disk Recovery | Medium | Even 'RAM-only' deployments usually have some persistent layer (boot medium/firmware/management controller), but that layer shouldn't contain browsing history if the provider's design is sound. |
| Hardware Tampering | Policy-Based | Strict policy: "We don't reuse hardware that police returns." |
| Live Memory Capture | Critical | The real risk isn't the unplugged box - it's a live acquisition (memory dump or hypervisor access) before the plug is pulled. |

What Should Users Do?
This news is developing, but here is the current guidance based on available information:
- For normal users: No urgent action is required based on current info. Continue using HTTPS and keep your software updated.
- For higher-risk users: Avoid using Netherlands (NL) exit nodes until more details emerge. Consider layering your connection (e.g., using Tor) if your threat model requires it.
- Everyone: Remember that no VPN can beat advanced traffic correlation by a state-level adversary monitoring both entry and exit points.
The Cold Boot Threat
Why standard raids fail
- Cold boot attacks involve freezing RAM chips to preserve data for minutes after power loss. This is niche and requires immediate physical access to the machine while it is still warm.
- Practically, if Windscribe Dutch authorities seize vpn server hardware by pulling it from a rack and transporting it to a police station, recovery is far less likely due to memory decay over time.
- Warrantless Seizure? If Dutch authorities seized a Windscribe VPN server without a warrant, the legal admissibility of any recovered evidence might be contested, though this does not help user privacy once the data is exposed.
The Real Risk: Live Capture
- The real danger isn't the unplugged box - it is a live acquisition.
- If an agency gains hypervisor access, compromises the BMC/iDRAC management interface, or correlates upstream traffic at the datacentre level while the server is running, RAM encryption offers little protection.
FAQs
Does "No Logs" mean absolutely no data is stored?
Not exactly. Windscribe says it doesn't keep identifying activity logs (websites visited, IP timestamps). However, like most providers, they retain limited account metadata such as "last used" date and bandwidth consumption to enforce free-tier limits.
Is user data safe if the server was seized?
If the server was powered off during seizure, user data stored in RAM would have decayed rapidly. The risk is significantly lower than with traditional hard-drive logging, though not theoretically zero if a 'Cold Boot' attack was performed immediately.
What is the 2021 Ukraine incident mentioned?
In 2021, Windscribe had servers seized in Ukraine. At that time, they acknowledged that the servers were not fully encrypted, a vulnerability they claim to have since fixed with their current RAM-only architecture.
SUMMARY BY ECH THE TECH FOX
You can criticise the "engagement farming" joke, but if the architecture holds up, you can't criticise the security. The authorities seized a box, but according to the tech specs, they didn't seize a single byte of user data. This incident serves as an unplanned audit of Windscribe's privacy claims.

BY MARTIN NEEDS
Director at Needsec LTD; Cybersecurity Expert; 10+ Years Experience
"From a forensic perspective, this seizure is a textbook example of why volatile memory is considered superior to encrypted disk storage for privacy services. Once the power chain is broken, the cryptographic keys and the data residing in the RAM modules decay within seconds at room temperature. If the Dutch authorities simply pulled the rack unit as described, they likely have a very expensive, very empty metal box."
